Introduction
Think back to 2018. Or maybe 2015. You probably signed up for a gaming forum to ask a question about a level you were stuck on. Or maybe you registered on a niche hobby site to download a specific file. You used your main email address, created a password, got what you needed, and never visited the site again.
You forgot about that site. But the internet didn't forget you.
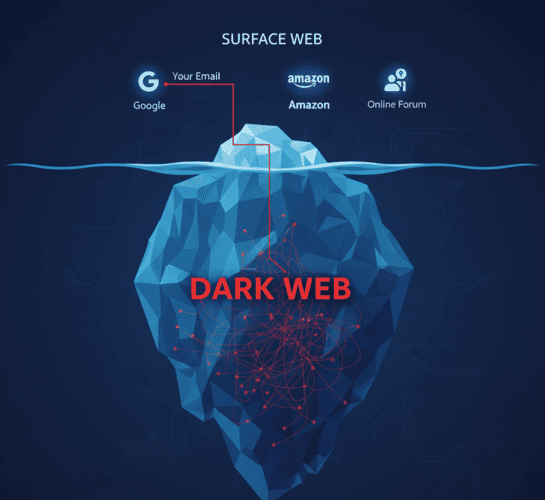
Years later, that dormant forum gets hacked. The attackers steal the entire user database, usernames, passwords and most importantly, email addresses. This database is then sold on the Dark Web. Suddenly, hackers halfway across the world have your primary email address and a password you might still be using elsewhere.
This isn't a rare horror story; it is a daily occurrence. In this article, we will explore the lifecycle of a data leak and show you why using your primary email on forums is a ticking time bomb and how TempMailM defuses it.
The Anatomy of a Forum Hack
Why are forums and small websites such dangerous places for your email?
-
Weak Security: Unlike Google or Facebook, which spend billions on security, the average hobby forum is often run by volunteers on outdated software. They are easy targets for "SQL Injection" attacks.
-
The "Database Dump": When hackers breach these sites, they don't just steal one account; they download the entire table of users. This is called a "database dump."
-
The Dark Web Marketplace: These dumps are packaged into "Combo Lists" (Email:Password combinations) and sold on Dark Web marketplaces. A list of 1 million valid emails might sell for as little as $50.
Once your email is on one of these lists, it is public property in the criminal underworld.
The Domino Effect: Credential Stuffing
You might think, "So what? I don't care if they hack my account on a knitting forum."
Here is the problem: Credential Stuffing.
Hackers know that humans are creatures of habit. If you used the password BlueSky123! on the knitting forum, there is a statistically high chance you used the same password (or a variation) for your Netflix, your PayPal, or your primary Gmail.
Attackers use automated bots to test that leaked email/password combination against thousands of popular websites.
-
They try it on Amazon.
-
They try it on Uber.
-
They try it on Coinbase.
If you used your real email on that "insignificant" forum, you gave them half the key to your digital kingdom. If you reused a password, you gave them the whole key.
The Solution: Segregation with Disposable Email
How do you protect yourself from a breach that hasn't happened yet? By practicing Email Segregation.
The rule is simple: If the service is not critical to your life, it does not deserve your real email.
When you use TempMailM to sign up for a forum or download site:
-
You Break the Link: The generated email (
[email protected]) has absolutely no connection to your real identity. -
The Leak is Contained: If that forum gets hacked 5 years from now, the hackers steal a temporary email address that was deleted 5 years ago.
-
No Credential Stuffing: Even if they try to use that email to hack other accounts, the email doesn't exist. The attack fails instantly.
You are effectively creating a "firewall" between the chaotic, insecure web and your personal, secure life.

How to Check If You Have Been Leaked
If you have been using your real email everywhere until now, you might already be compromised. Here is how to check and fix it:
-
Use "Have I Been Pwned": Visit haveibeenpwned.com. This is a safe, legitimate site run by security experts. Enter your email. It will tell you exactly which data breaches your email appeared in.
-
Change Passwords Immediately: If you are in a breach, change your passwords on every site where you reused that combination. Use a Password Manager to generate unique passwords.
-
Start Using Temp Mail TODAY: You can't change the past, but you can protect the future. Stop adding your email to new databases.
Conclusion: Don't Be Low-Hanging Fruit
Hackers are like predators; they look for the easiest prey. The person who uses the same email and password for everything is the easiest target on the internet.
By using TempMailM for your daily sign-ups, verifications, and casual browsing, you remove yourself from the target list. You make yourself "invisible" to the bots and scrapers that fuel the Dark Web economy.
Your primary email is for you and the people you trust. For everyone else, there is disposable email. Make the switch today and sleep better knowing your data is safe.
