Introduction
In the physical world, you wouldn't walk around wearing a nametag with your home address, phone number, and social security number written on it. Yet, in the digital world, millions of us do exactly that every day. How? By using our primary email address for everything.
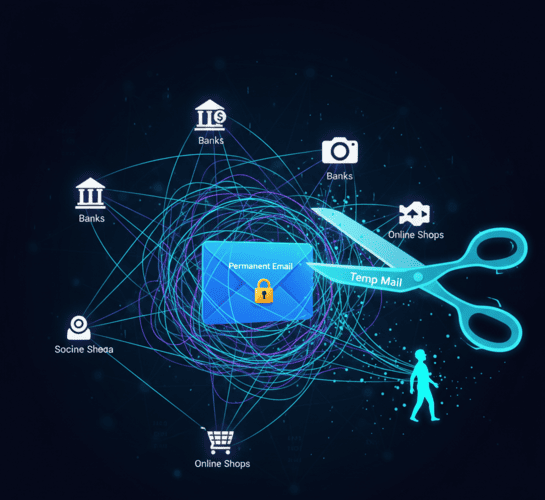
Your email address is no longer just a way to send messages. It has become your Unique Digital Identifier (UDI).
-
Google uses it to build your ad profile.
-
Facebook uses it to find your friends.
-
Data brokers use it to link your shopping habits to your voting records.
Every time you type your real email into a sign-up box, you are leaving a breadcrumb. Enough breadcrumbs, and anyone from advertisers to cybercriminals can follow the trail back to your front door.
If you want to reclaim your privacy, you need to stop leaving these crumbs. The most powerful tool for this task is a Fake Email Generator. In this guide, we will explore how this simple tool acts as a cloak of invisibility for your online identity.
The "Master Key" Problem: Why Your Email Matters
Why is protecting your email so critical? Because it is the "Master Key" to your digital life.
Think about it:
-
It Connects Everything: Your Amazon account, your bank, your Netflix, and your medical portal all share one common link: your email. If a hacker cracks your email, they crack everything.
-
It Enables Cross-Site Tracking: Have you ever looked at a pair of shoes on one site and seen ads for them on Instagram five minutes later? That’s often because your email address (even a hashed version of it) was used to match your identity across platforms.
-
It is Permanent: You might change your phone number or move houses, but most people keep the same email address for 10 or 20 years. This creates a massive, unbroken history of your life online.
Using a fake email generator like TempMailM breaks this chain. By using a different, temporary address for each interaction, you prevent these data points from being connected.
How a Fake Email Generator Protects You
Let's look at specific scenarios where generating a fake email creates a layer of armor around your identity.
1. Preventing "Doxxing" and Harassment
The internet can be a hostile place. If you engage in debates on political forums, comment on controversial news articles, or play competitive online games, you are a target. Trolls can use your email address to find your real name, your employer, or your address (a practice known as "Doxxing").
-
The Fix: Never use your real email for public-facing accounts. Use a disposable address. If someone tries to track you, the trail ends at a deleted inbox.
2. Avoiding Data Breach Fallouts
"Company X has suffered a data breach. 50 million emails leaked." We see this headline every month. If your main email is in that database, you are on a target list for life.
-
The Fix: If you used a TempMailM address to sign up for that random app three months ago, it doesn't matter if they get hacked today. The email they stole is worthless. Your real identity is safe.
3. Stopping Profile Building
Data aggregators (companies like Acxiom or Equifax) make money by building dossiers on citizens. They know you like cats, buy organic food, and travel to Spain. How? By aggregating data from every newsletter and loyalty program you join.
-
The Fix: When you use a fake email for these signups, you feed "junk data" into their system. You poison the well. They can't build an accurate profile of you because the data points don't connect to a single person.
Advanced Strategy: The "Burner Identity" Protocol
For those who are serious about privacy, here is a protocol used by privacy advocates and cybersecurity experts. It involves using TempMailM as part of a broader strategy.
Step 1: The One-Time Purchase Buying a digital gift card or a game key from a site you don't fully trust?
-
Use a fake email generator for the account.
-
Use a virtual credit card (like Privacy.com) or crypto for payment.
-
Result: The merchant knows nothing about you.
Step 2: The Social Media "Alt" Account Want to check Twitter/X or browse LinkedIn anonymously?
-
Generate a temp mail.
-
Register the account.
-
Verify the code instantly on TempMailM.
-
Result: You can view content without the platform linking it to your professional profile.
Step 3: The "Review" Bomber Want to leave an honest negative review for a bad product but afraid of retaliation from the seller?
-
Use a disposable email to verify your review account.
-
Result: Your honest feedback is public; your identity is private.

What a Fake Email Generator Cannot Hide
It is important to be realistic. While TempMailM hides your email identity, it does not hide your internet connection.
-
Your IP Address: The website can still see your IP address (your digital location). To be truly anonymous, you should combine TempMailM with a trustworthy VPN (Virtual Private Network).
-
Browser Fingerprinting: Websites can identify you by your browser version, screen resolution, and fonts. Using a privacy-focused browser (like Brave or Firefox) helps here.
The Privacy Trinity:
-
VPN: Hides where you are.
-
TempMailM: Hides who you are.
-
AdBlocker: Hides what you see.
Conclusion: Privacy is a Choice
In 2026, privacy is not the default setting; it is a choice you have to make actively. Big Tech companies are betting that you will be too lazy to protect your data. They are counting on you handing over your "Master Key" email address because it's convenient.
Prove them wrong. Using a fake email generator takes literally seconds no registration, no cost, no hassle. But the value it provides keeping your identity yours and yours alone is priceless.
Don't let your digital life become an open book. Use TempMailM, generate a shield, and browse the internet on your own terms.
