Introduction
When you use a fake name and a disposable email address to sign up for a website, it feels like you have successfully put on a digital disguise. You bypassed the form, downloaded the file you needed, and left without giving up your precious personal data.
But for the privacy-conscious internet user, a lingering question remains in the back of their mind: "Am I truly untraceable? Can this temporary email be tracked back to me?"
The short answer is: It makes tracking you exponentially harder, but it is not a magic invisibility cloak on its own.
To truly master your online privacy, you need to understand how digital tracking works, what a disposable email actually hides, and what it leaves exposed. In this deep dive, we will tear apart the mechanics of email tracking and show you how to build an impenetrable wall around your identity using tools like TempMailM.
The Invisible Spies: How Normal Email Tracking Works
Before we analyze temporary emails, let's look at why your primary email (Gmail, Outlook) is a privacy nightmare.
Marketers and corporations don't just send emails into the void; they track everything you do with them. They use a sinister but brilliant piece of technology called a Tracking Pixel (or Web Beacon).
A tracking pixel is a transparent image, usually exactly 1x1 pixel in size, embedded invisibly inside the HTML code of an email. Because it is an image, your email client has to download it from the sender's server to display the message.
The moment your computer downloads that invisible pixel, the sender's server logs:
-
Exact Time: When you opened the email.
-
Device Info: Whether you are using an iPhone, a Mac, or a Windows PC.
-
Your IP Address: Your digital location (which reveals your city, internet provider, and sometimes your exact neighborhood).
-
Forwarding: If you forwarded the email to someone else.
If you are using your real email address, all this behavioral data is tied directly to your real name and identity.
How TempMailM Breaks the Tracking Chain
When you use a disposable email address, you disrupt this surveillance machinery in a fundamental way: You sever the link to your identity.
Even if an email sent to your TempMailM inbox contains a tracking pixel, and even if that pixel loads, the data it sends back to the marketer is effectively useless.
-
The Marketer Sees: "Email address
[email protected]opened the email at 4:00 PM." -
The Reality: They do not know who
randomxyzis. They don't have your name, your primary email history, or your purchasing profile. You are a ghost. You have fed them "junk data" that pollutes their tracking metrics.
Furthermore, reputable disposable email services act as a buffer. The email is received by our servers first. When you view the text on our platform, you are in a secure web environment, minimizing the risk of aggressive scripts running directly on your local machine.
The Reality Check: What Disposable Email Does NOT Hide
This is where we must be completely honest. A temporary email protects your Inbox Identity, but it does not hide your Network Identity.
If a law enforcement agency or an incredibly sophisticated tracking network wanted to find you, relying only on a temporary email is not enough. Here is what is still visible when you browse the internet:
1. Your IP Address is Exposed to the Website
When you go to a forum to register using your TempMailM address, that forum still logs the IP address of the computer you are using to connect to their site. If you do something illegal, authorities can subpoena the website for that IP address, and then subpoena your Internet Service Provider (ISP) to find your physical house.
2. Browser Fingerprinting
Modern websites don't just look at IP addresses. They look at your specific combination of screen resolution, installed fonts, browser version, and operating system. This creates a highly unique "fingerprint." Even if you use a fake email, the website might recognize your browser fingerprint from a previous visit where you did use your real name.
3. Cookies
If you don't clear your browser cookies, a website can recognize you. Using a temporary email while logged into your Google account in the same browser window defeats the purpose, as tracking scripts can cross-reference the activity.
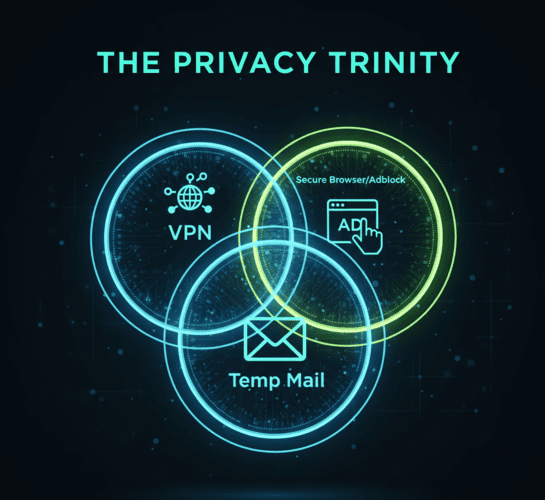
The Ultimate Anonymity Stack: The "Privacy Trinity"
If you want to be truly untraceable whether you are a journalist protecting sources, a whistleblower, or just someone who demands absolute privacy you must use the Privacy Trinity.
To become a true digital ghost, combine these three tools:
-
A No-Log VPN (Virtual Private Network): This masks your IP address. It makes it look like you are browsing from Switzerland or Japan, hiding your physical location from the websites you visit.
-
A Privacy-Focused Browser: Use browsers like Tor, Brave, or Firefox with strict tracking prevention enabled. Always use "Incognito/Private" mode to prevent cookies from being stored. This defeats Browser Fingerprinting.
-
TempMailM (Disposable Email): This hides your personal identity. When the website asks "Who are you?", you give them a burner address.
When you combine all three: The website doesn't know where you are (VPN), they can't recognize your device (Private Browser), and they don't know your name or inbox history (Temp Mail). You are invisible.
Conclusion: Context is Everything
So, can temporary emails be tracked? The email address itself is a dead end. It cannot be linked to your real identity unless you explicitly provide that link.
However, your internet connection can be tracked.
For 99% of people those just trying to avoid newsletter spam, get a 10% discount code, or bypass a newspaper's paywall TempMailM is more than enough protection. It stops the marketers dead in their tracks.
But if your goal is absolute, bulletproof anonymity against sophisticated tracking, remember that a disposable email is just one crucial piece of the armor. Pair it with a VPN, and reclaim your digital freedom.
